Enhance Data Protection With Universal Cloud Storage
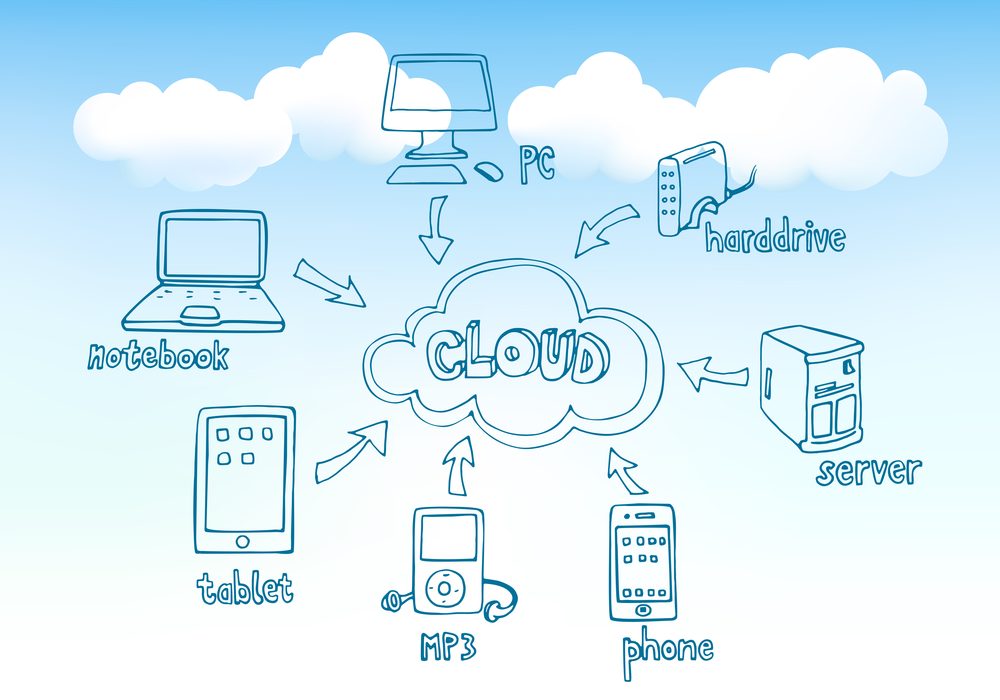
Universal cloud storage space provides a compelling option to boost information protection procedures through its robust attributes and capabilities. By harnessing the power of encryption, accessibility controls, and calamity recovery techniques, global cloud storage space not only safeguards sensitive info yet additionally guarantees information availability and integrity.
Advantages of Universal Cloud Storage Space
Checking out the advantages of executing Universal Cloud Storage space exposes its effectiveness in enhancing information protection steps. Among the essential advantages of Universal Cloud Storage space is its ability to give a centralized and protected system for keeping data. This centralized method enables easier accessibility and monitoring of data, bring about boosted efficiency in information handling procedures. In Addition, Universal Cloud Storage space uses scalability, permitting services to quickly increase their storage capability as their data needs expand, without the demand for considerable investments in framework.
Moreover, Universal Cloud Storage boosts data security via functions such as encryption, accessibility controls, and automated backups. Automated back-ups guarantee that data is frequently backed up, reducing the threat of data loss due to crashes or cyber attacks.
Secret Attributes for Data Protection
Trick safety attributes play a vital duty in securing information integrity and confidentiality within Universal Cloud Storage space systems. Security is a fundamental feature that guarantees data saved in the cloud is protected from unauthorized gain access to. By securing information both en route and at rest, sensitive info stays safe and secure even if intercepted. Furthermore, normal information back-ups are important for stopping information loss as a result of unpredicted occasions like system failings or cyber-attacks. These back-ups should be stored in diverse locations to improve redundancy and integrity.
Authentication mechanisms such as multi-factor authentication and solid password needs include an additional layer of safety by confirming the identity of users accessing the cloud storage. Breach discovery and prevention systems continuously monitor for any kind of dubious tasks and help mitigate possible safety breaches. Furthermore, audit logs and task surveillance make it possible for companies to track data accessibility and alterations, helping in the detection of any kind of unauthorized activities. In general, these key attributes collectively add to robust information security within Universal Cloud Storage systems.
Applying Secure Gain Access To Controls
Safe accessibility controls are pivotal in making certain the integrity and privacy of data within Universal Cloud Storage space systems. By applying secure access controls, organizations can regulate who can check out, customize, or remove information saved in the cloud.
An additional essential part is authorization, which determines the level of access given to validated individuals. Role-based gain access to control (RBAC) is a typical technique that designates certain authorizations based upon the functions individuals have within the organization. Furthermore, executing multi-factor authentication adds an extra layer of safety and security by requiring users to provide numerous kinds of confirmation prior to accessing data.
Routine tracking and bookkeeping of gain access to controls are important to spot any kind of questionable activities immediately. By continuously reviewing and fine-tuning access control plans, companies can proactively secure their data from unapproved access or violations within Universal Cloud Storage atmospheres.
Data File Encryption Best Practices
A robust information encryption approach is vital for boosting the security of details stored in Universal Cloud Storage find here systems. Information encryption finest techniques involve securing information both en route and at remainder. When information is in transportation, making use of protected interaction procedures such as SSL/TLS makes certain that information exchanged in between the customer and the cloud storage is encrypted, stopping unapproved access. At rest, data need to be secured using strong file encryption algorithms to secure it from being endangered if the storage space infrastructure is breached.
Trick monitoring is another essential element of data file encryption ideal techniques. Applying correct key management procedures ensures that encryption tricks are firmly saved and taken care of, protecting against unapproved accessibility to the encrypted data. On a regular basis upgrading encryption keys and rotating them aids boost the protection of the information gradually.

Backup and Catastrophe Recovery Methods
To make certain the connection of procedures and protect against data loss, companies have to develop robust backup and disaster recuperation approaches within their Global Cloud Storage systems. Backup strategies should consist of normal automatic backups of crucial information to numerous places within the cloud to reduce the risk of information loss (linkdaddy universal cloud storage press release). By carrying out extensive backup and calamity healing strategies, companies can improve the resilience of their information administration practices and decrease the effect of unexpected information occurrences.
Conclusion
Finally, universal cloud storage uses a robust remedy for improving information safety through attributes like encryption, access controls, and back-up strategies. By carrying out protected accessibility controls and complying with information file encryption ideal methods, companies can efficiently shield sensitive info from unauthorized gain access to and go to this site protect against data loss. Backup and catastrophe recovery techniques better strengthen information security steps, making certain data stability and schedule in the event of unanticipated incidents.